Since the beginning of the year, Japanese one-click fraud scammers have continued to pump new apps onto Google Play and the market has struggled to keep itself clean. Though many are removed on the day they are published, some remain for a few days. Although they have short lives, the apps must provide ample profit for the scammers as they show no signs of halting their development of new ones. Their tactic of abusing the search function on Google Play allows their apps to be easily bumped to the top of keyword searches. A test search carried out by Symantec resulted in 21 out of 24 top hits being malicious apps.
Figure 1. Search with only 3 out of 24 results not malicious
The scammers have been persistent as well, publishing apps almost daily amounting to over 1,200 apps in total being published over the last seven months.
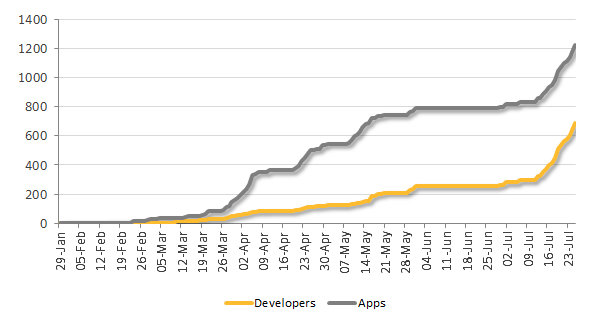
Figure 2. Activity over seven-month period
Because of the success the scammers appear to be having, it seems a new player has come along to try their luck on the market. The new scam is a variation on the typical one-click fraud we see in Japan. The new type not only requires clicks, but it also requires users to send an email in order to register to become a member of a service, call a given phone number to acquire a password, and enter the password to log into the fraudulent site. That’s quite a bit of work to get through just to be scammed. Once the user successfully logs into the site, they are charged an annual fee of 315,000 yen, which is equivalent to approximately US$3,150, for watching online adult videos without any obvious prior warning of the fee.
Figure 3. Three developers previously posting malicious apps
The app is downloaded from Google Play.

Figure 4. App download page
Once the app is opened, the browser is launched to open an adult video site.
Figure 5. Adult video site
If the user tries to play a video from the adult site they are requested to register to become a member in order to watch all site’s videos.

Figure 6. Registration request page
An email is automatically drafted when the ‘send email’ button is clicked. All the user needs to do is to click on the “send” button.
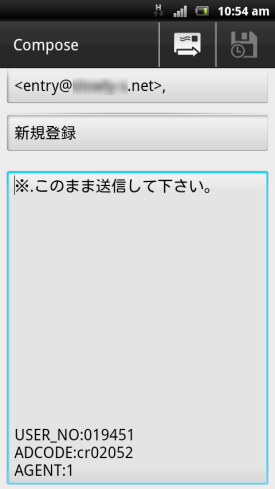
Figure 7. Automatically drafted email
Shortly after, the service returns an email containing a link.

Figure 8. Email containing link
Clicking on the link takes the user to another service on a different site.
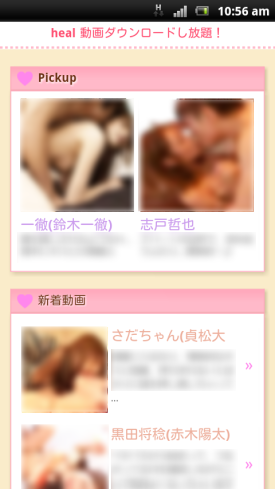
Figure 9. Another adult video site
This time when a video is selected, the user is asked to enter a password to log in.

Figure 10. Password request page
Clicking on ‘confirm password’ prepares the phone to make a call to a pre-determined number.
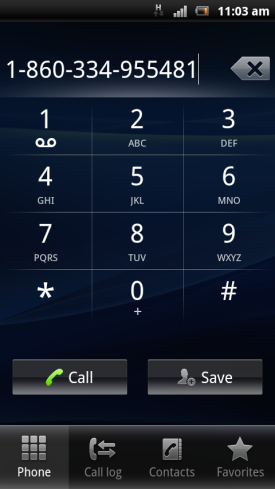
Figure 11. Phone preparing to call a pre-determined number
When the call is made to this number, an automated message tells the user the password. After logging into the site with the given password, a page appears on the browser informing the user of the registration details as well as notifying them of a whopping 315,000 yen annual fee due in three days.

Figure 12. Registration and annual fee details
I don’t recall reading anything about the service requiring an annual fee…although, wait a minute, there is a hidden link to a EULA on the page where the password is entered. The sentence where the link is states that to use the site you must be an adult who has agreed to the user agreement. The link is very faint compared to other text on the page.
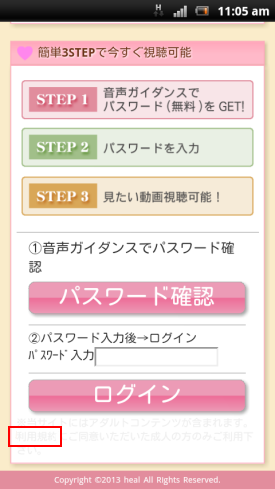
Figure 13. Almost hidden link to EULA (highlighted in red box)
It does in fact state that the service has an annual fee in the EULA, if you can eventually find it that is. There are some very sneaky tactics being used here!
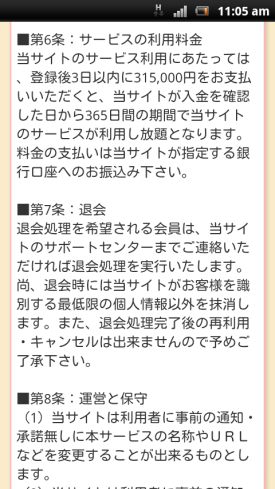
Figure 14. EULA
Because these apps only launch the browser to open certain sites, which request users to take additional steps to reach the final destination, it can almost be impossible for any system to confirm anything malicious about these apps. The manual steps required in this scam is another strategy used to keep the apps on the market as long as possible. Human analysis may be the only way to discover these sorts of apps. We have so far confirmed over 100 of these apps published on Google Play since the beginning of July. At the time of writing, there are currently still 30 apps, published by three developers, still available on the market. Symantec continues to inform Google about these apps so that they can be removed. Hundreds of users have downloaded the apps, but the actual number could potentially be over a thousand. It is unknown how many people have actually been tricked into paying the fee. The apps discussed in this blog are detected by Symantec products as Android.Oneclickfraud. Please take precaution when downloading apps, regardless of where they are hosted and we recommend using our Norton Mobile Security to help protect you.