10 Ground Rules for Red Teams
An effective Red Team offers huge value to your defensive strategy, but you have to be prepared to face up to some hard truths
Imagine a team in your organization that could simulate your enemies and improve your resilience to their tactics and techniques.
For Symantec, that’s us. We’re the Red Team, a small but highly-skilled team of offensive security professionals. We apply real-world attacker techniques to test and continuously improve Symantec’s internal environment and the products we sell.
Red Teams are highly attractive to CSOs, not least because our work goes to the heart of the question that keeps them up at night: “Are we protected?”. It’s a powerful resource to have but given the sensitivity of what we do, many CSOs wonder what measures to put in place to ensure they and other senior executives feel comfortable.
Here’s what I’ve learned from setting up Red Teams at several organizations.
10 Ground Rules for Red Teams
Clear Purpose
The organization needs to start from a common understanding of what the Red Team’s mission and purpose is.
Our job is not to “find all the vulnerabilities”, but to determine, via adversary emulation, which attack behaviors would allow legitimate attackers to achieve specific objectives via cyber, physical and human means.
A common mistake companies make is to become overly system-specific with their Red Team (there are other teams for this), and to neglect the organization’s crown jewels and the controls protecting them. An objective-based adversary simulation approach ensures your Red Team maintains focus.
Red Teaming is ultimately about two things - determining how vulnerable we are by uncovering vulnerabilities such as misconfigurations, bugs and exploitable conditions, and identifying blind spots in our ability and our readiness to react.
Align to the Organization’s Appetite
Before you start, it’s vital to gauge your organization’s appetite for the sort of campaigns and activities you will run.
This isn’t a question of cost or resources, but of the company being prepared to face potentially hard truths about its security posture and being willing to address weaknesses and gaps when they are identified.
It’s useful to discuss ahead of time with your executives and key stakeholders what red teaming activities will entail, and equally what it doesn’t entail (e.g. testing specific systems).
Don’t Operate in a Bubble
Red Team activities are, by definition, somewhat secretive. Our job is to behave like real-world attackers to test the true security posture and response of our organization. At Symantec, our leaders have given us the autonomy and freedom we need to run our campaigns in a realistic fashion (i.e. without tipping off defenders) and report what we find.
At the same time, Red Teams can’t afford to operate in a bubble.
We’re helped by strong relationships and support from other teams like our Blue Teams, legal, physical security, risk and various lines of our business. For instance, we engage legal during planning phases to ensure operations won’t introduce undesired legal or regulatory risk. We give our physical security teams advance notice of any activity that could result in escalations to law enforcement.
We exist to be the sparring partner of our opposite number Blue Teams. We work closely with them to help them achieve their goals in defending the organization.
Be Strategic
The skills of a Red Team can be misdirected to ad-hoc requests by business units. Or worse, they can be used as a political weapon to quash certain projects. These are less-optimal uses of a team’s skills and abilities.
Comprehensive annual planning, with strategic inputs from our partner teams working in threat intelligence and cyber simulations, helps our Red Team align activities to the bigger picture and what’s important to Symantec.
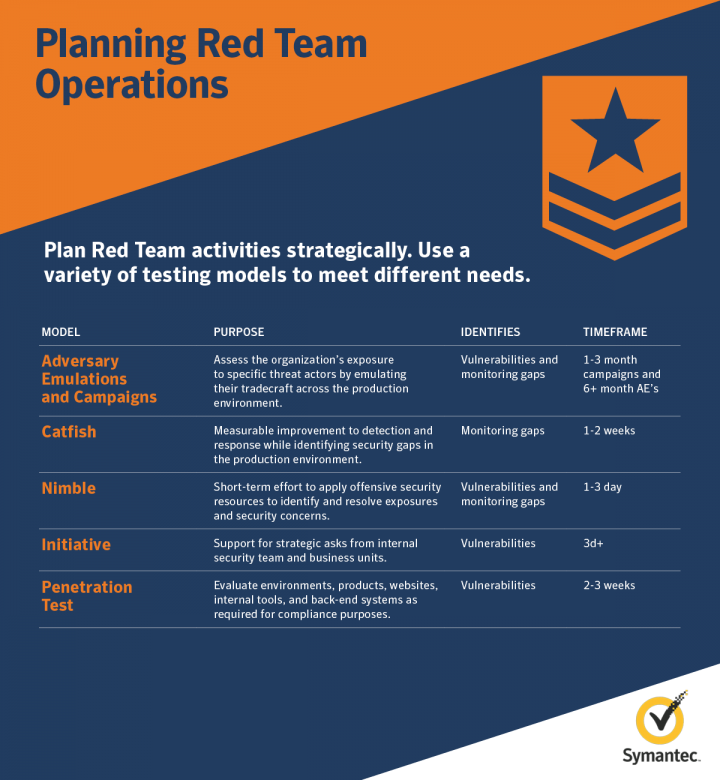
Plan Operations Meticulously
Given the sensitivity of what we do, we’re meticulous about the planning and approach for each operation.
Clear rules of engagement and objectives are defined for each operation up front, including processes for out-of-band reporting of any critical findings. Think carefully about participants in your operations – limiting “insiders” is key to maintaining realism.
Never Negatively Impact Security Posture
Our Red Team enforces a set of guiding principles when planning and executing operations. Abiding by this code is vital to maintaining the confidence and comfort of our executives.
These principles include “proving appropriately” – doing no more or no less than the scope and objectives of each campaign – and taking appropriate security precautions during operations, such as protecting and encrypting data.
Most importantly, we never negatively impact security posture. For example, we avoid making actual configuration changes on production systems that could open them up to legitimate attacks. We prove the potential for such an attack, rather than actually disabling a key control.
Peer Monitoring
Acknowledge that people can and do make mistakes. A second or third set of eyes on a key phase of an operation helps catch mistakes before they happen.
Peer monitoring also helps ensure Red Teamers stay within the rules of the operation and provides staff that can act as witnesses in the event there are concerns about what occurred during an operation.
Formalize Reporting and Track your Risks
While the fun might be in executing out the campaigns, Red Teams must also be thoughtful about reporting – this is where the organization sees the value of your efforts.
We progressively brief key teams in the organization – legal, security leadership, business leadership, risk and audit teams and control owners – via a formal structured “outbrief” process.
Using standardized risk definitions and formally tracking our findings in our risk registers is vital for illustrating larger trends and patterns within the organization and for driving actual change from the work of Red Teams.
Hire for Diversity
If we want to effectively and accurately simulate the cyber-attacks of today and tomorrow, we need a team that boasts the depth, breadth and diversity of offensive security skills.
I strive to ensure my team reflects a diversity of backgrounds in security and technology, for example, people with experiences across blue team, architecture, software development and other disciplines.
At the same time, a good red teamer is more than the sum of their specific set of skills and expertise. When I’m assessing prospective talent, integrity, passion and chemistry usually come first.
Given the access to data we obtain during operations, in addition to thorough vetting I also recruit primarily from circles that I trust.
Be Humble
We strive to be humble in our reports and remember to highlight the positives.
This includes a determination to give back. The Red Team community is filled with people who are passionate about advance the tradecraft, and our team has benefited from this community in countless ways. As a program, we seek to contribute back to red team community by sharing lessons and best practices. This aligns to the Symantec security team’s vision to be standard bearers for security practice.









We encourage you to share your thoughts on your favorite social platform.