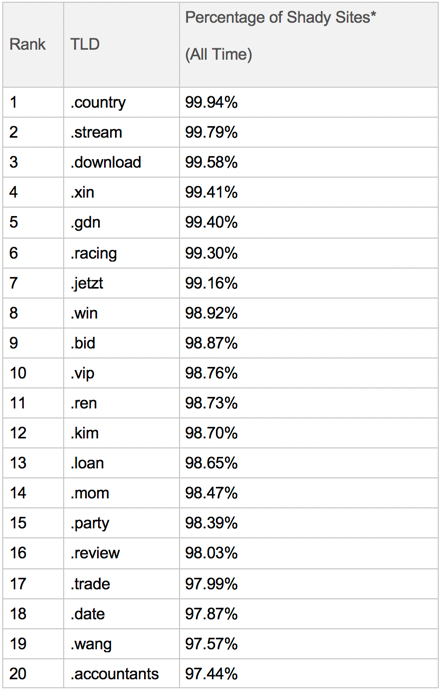
The "Top 20": Shady Top-Level Domains
Our latest report on the most suspicious TLDs in existence today as Internet scammers and hackers continue to try and game the system
[Editor’s Note: This is #23 in our ongoing series focusing on Top-Level Domains (TLDs) with high percentages of malicious or otherwise shady domains among their registrations. Links to the previous posts are found at the bottom of the page.]
Every January we calculate and then publish a "Top Twenty" list of the “shadiest” TLDs in the hope that highlighting the vast amounts of abuse will prompt some changes in behavior. Occasionally, it works and a TLD registry will reach out to ask how to screen out some of the riff-raff. More often, though, the abuse continues as Internet scammers and hackers seek to game the system. But at least folks outside of our customer base now have some additional warning about the risks they face.
Accordingly, here are the Top Twenty Shady TLDs, as of the close of 2017.
Caveats
As always, we caution against reading too much into the relative positions of TLDs on this list. Rankings are very fluid from quarter to quarter. Also, we are not advocating setting up policy to block all domains on all of these TLDs. Any such recommendation would come only after more research into a TLD. In particular, .xin is rather popular in China, as is .kim in South Korea, and it would not be wise to automatically block such domains if you do any business there. Also, several TLDs have percentages based on much lower numbers of domains than some of the other TLDs in the list.
In general, it's better to leave shady domain blocking up to the professionals.
Low .Bid-ders
I've had an eye on the .bid TLD for some time. While it wasn't in 2016's Top Twenty list, it's been on the leader board for some time, and moved into the Top Ten in the middle of 2017. It dropped a bit from its #7 ranking in Q3 to #9 in Q4, but it still shows up a lot in traffic.
To get a sense of how it's being abused, I did a deep dive into a week of our December worldwide WebPulse traffic logs, and pulled out a list of the 100 most popular .bid sites. Here is how the traffic broke down:
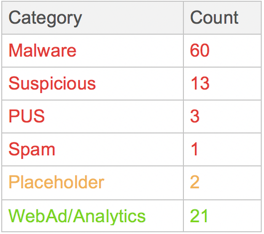
So that's "only" 77% - 79% shady, which isn't as bad as the historical value (98.87%) shows.
However, the above numbers need a bit of clarification. On the Internet, subdomains of a parent domain are treated as (potentially) separate hosts --they may all be located on the same IP, and use the same server, or each may be on a completely different IP and/or server. For example, 16 of those 21 WebAd/Analytics sites in the table were subdomains of a single parent.
Still, it's clear that there is a considerable amount of WebAd/Analytics traffic in the .bid space -- it's a rather natural TLD for this use -- and that would need to be factored into a decision on how to handle .bid URLs by default.
Hunting for Examples
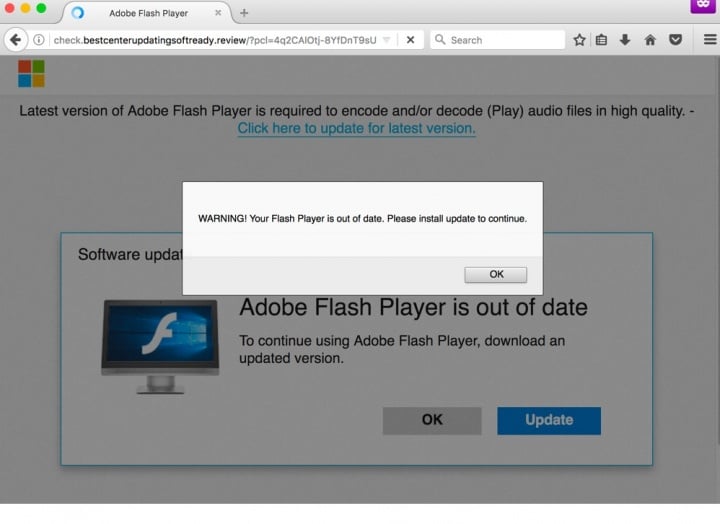
Seeing so many Malware ratings in the database, I was curious as to what we were catching. The database notes show that it mostly malware downloads detected and detection of "shady WebAd networks" (i.e., probable malvertising -- leading to those downloads).
It would have been nice to grab some samples, but all of those malicious sites were dead by the time I was building the table. So, I had to go hunting for fresh stuff.
Mostly, the sites I found looked like the Scam/PUS end of the Malware spectrum:
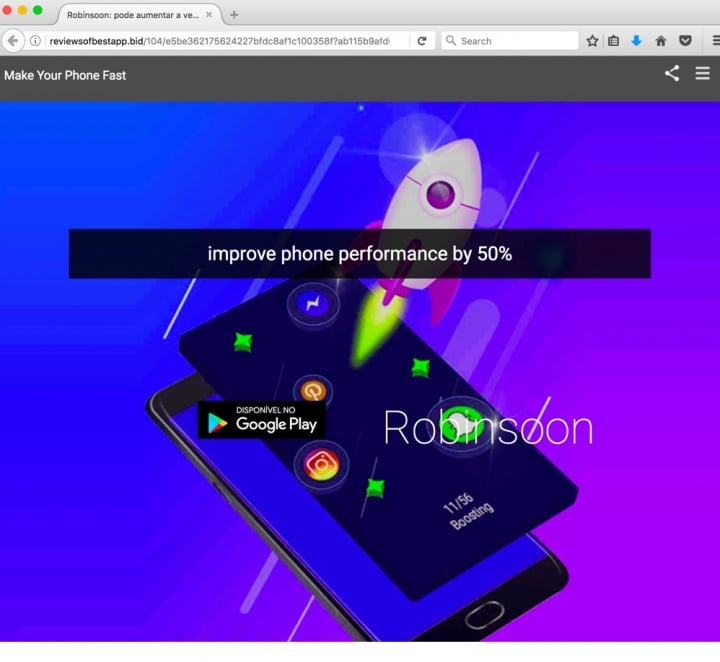
There is, of course, a strong link between that Scam/PUS world and the Spam that brings in the victims. A great illustration is one of the junky domains (newsflash1online.bid), which didn't even have an actual Web page in its root, but was instead a directory listing over 40 Spam/Scam/PUS offer pages, such as these samples:
In summary, there don't appear to be many legitimate/useful sites on .bid, unless you're the sort who counts WebAd/Analytics sites as useful.
-C.L.
@bc_malware_guy
P.S. For easy reference, here are the links to the earlier posts in our "Shady TLD" series:
.country
.kim
.science
.gq
.work
.ninja
.xyz
.date
.faith
.zip
.racing
.cricket
.win
.space
.accountant (and .realtor)
.top
.stream
.christmas
.gdn
.mom
.pro
.men







We encourage you to share your thoughts on your favorite social platform.