Don’t Leave Security Holes in your (AWS) Buckets
Misconfigured AWS S3 buckets can lead to the accidental disclosure of confidential data. And it’s happening more often than you might think
As December vacations beckoned, people looked forward to spending time with families and friends during the holidays. But their teeth would have been set on edge had they known what was happening with their personal data stored on the cloud.
A misconfigured Amazon Web Services (AWS) S3 cloud storage bucket had publicly exposed information belonging to some 123 million households, leaving interlopers free to rifle through a trove of personal data. Unfortunately, this wasn’t a one-off. AWS S3 buckets are often accidentally left “world viewable,” resulting in the accidental disclosure of confidential data to everyone.
Similar issues have plagued sophisticated security organizations – including the US Army's Intelligence and Security Command, which was similarly found to have been leaking classified and sensitive data.
A common misconfiguration allows anyone with the AWS credentials to access sensitive company files used by applications. This error can occur when someone’s setting permissions on a top-level folder – and when they’re using subfolders, they may not even realize the information is being exposed. From that point, an attacker doesn’t even need to do anything clever to get a look at your data.
That’s just one issue. When it comes to securing cloud storage, companies need to understand that this is a lot different than building an on-premises defense. They face myriad threats that they may have never faced before. For example, malicious hackers are now able to assemble malware and infiltrate a company’s cloud in stages.
Open Season on Cloud Storage
Savvy hackers have come up with a grab bag of similar tricks to fool most anti-malware programs, which are not storage-specific. For instance, these programs will simply give up when it comes to vetting very large files – which is exactly what attackers desire since that allows them to evade anti-malware scans. There’s a new constellation of threats facing cloud storage. Consider, for example, the following:
- Malware persistence: Malware no longer restricts itself to looking at persisting in files on endpoints or registries on endpoints. It’s become increasingly able to hide in shared storage. Even when users reboot their computers, the malware can still resurrect itself from the registry or file system.
- Day-1 Incursion: Re-scanning of storage files helps where malware incursions occur before a day zero disclosure. But unless there is a subsequent remediation and re-scan with updated definitions you run the risk of new infections.
- Unscannable Network Files: Attackers are finding particular success evading detection by using deeply nested larger container files such as .zip, .tar. , .gz, and .bz. When these files are larger than 10MB, they often don’t receive scans and serve as springboards for new attacks on the network.
These and other changes in the threat landscape are all the more reason why you need storage security solutions that can automatically block attackers and plug any holes inadvertently left open.
Prevent Your Company from Kicking the Bucket
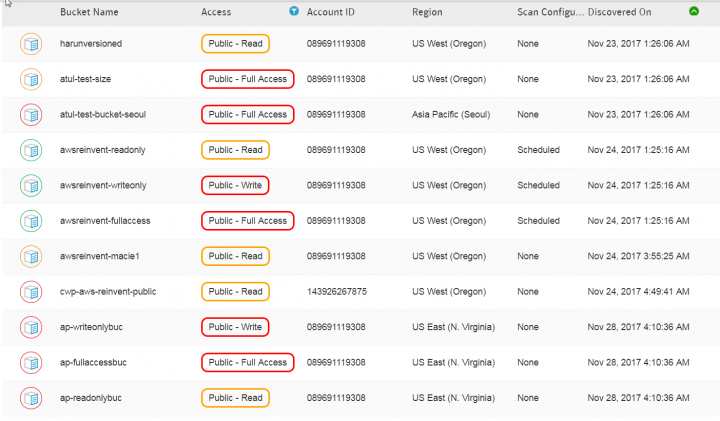
Symantec CWP provides compute, storage and container (docker) security in a single CWP console.
CWP-Storage includes malware protection, access visibility, quarantine management and remediation policy. Customer data stays in the customer’s custody and remains confidential – along with the convenience of auto-scaling.
Bottom line: As more companies move their storage to the cloud, attackers are moving to the cloud as well. For companies seeking to reap the economic and operational benefits of the cloud, make sure your storage is secure. All it takes is one small mistake to blow a hole in your defense as wide as the Grand Canyon.
If you found this information useful, you may enjoy:
Symantec Cloud Workload Protection for AWS Compute and Storage








We encourage you to share your thoughts on your favorite social platform.