Symantec Mobile Threat Defense: Smarter Incident Classification
One small step in content manipulation classification can be one giant leap for threat accuracy and enterprise mobile security efficacy
Behind the scenes of every modern enterprise is a security team responsible for keeping the organization and its employees safe from cyber threats. With the threat landscape constantly growing and becoming more complex, the security tools introduced to protect organizations are also expanding and growing more complex, especially from a management perspective. The amount of data, alerts, vulnerabilities, attacks and actions that need to be tracked and managed is immense, if not overwhelming, for most security teams, which are understaffed as it is.
Amid the flood of information, how can CISOs and their teams differentiate between the high-severity and lower-risk threats, so they know which ones to tackle first? Even with the best tools at their disposal, security professionals can’t do their jobs effectively if they don’t know where to focus their efforts.
The Grey Zone of Content Manipulation
We believe security tools should come with already-built-in mechanisms to help admins zero in on significant threats. A Forbes article from last year pointed out that, “In order to perform their jobs well, practitioners need a more curated selection of high-priority threats and the appropriate contextual information to mitigate them.”
One particular attack vector where something like threat curation or more effective filtering can go a long way, is mobile “content manipulation” attacks. Content manipulation occurs when attackers modify the response from a server that a device attempts to access, which can result in the defacement of a website, change in an app’s behavior, or even exploitation of a vulnerability on a victim’s device. Website owners and app developers have little control over content manipulation attacks on their centralized website server; attacks can occur autonomously at any location.
Once attackers have control over the network, they can use content manipulation as a vehicle to deliver a malicious payload via a browser or change a request that an app makes, enabling them to completely take over a device.
But content manipulation is not black or white in terms of malicious intent. For example, “web acceleration” software can be beneficial to Internet users because it improves website load time by injecting scripts that access cached versions of the site. Since it presents cached, rather than original, site resources it is considered a form of content manipulation, even if it is not malicious.
Some mobile threat defense (MTD) solutions – a category of enterprise security products used to detect and protect against threats affecting mobile devices – can detect content manipulation activities on the network. The problem is that they often don’t distinguish between the low-risk and high-risk threats. Admins and end-users are alerted whenever an anomaly is detected, even if it’s a case of web acceleration or other activities that may not pose serious risk to an organization. The alerts can pile up, with admins often unable to respond to real threats in a timely manner because they are distracted by lower-risk incidents.
Finding the Needle in a Haystack
At Symantec, we realized we were providing only part of the security picture when we alerted admins on content manipulation incidents. If we wanted to help them focus on the incidents that posed real risks, we needed to go deeper.
The team at Symantec Endpoint Protect Mobile (SEP Mobile), Symantec’s own mobile threat defense solution, initiated advanced, ongoing research in which we’re carefully analyzing millions of content manipulation incidents across our user base. Based on a granular inspection of common characteristics and variations in manipulated content, we’ve already classified 90% of all incidents according to patterns such as: web acceleration, content filtering, ad blocking, ad injection, and others. These classification patterns enable a more accurate determination of an incident’s risk. Content manipulation incidents that we can classify receive an accurate risk score. If the manipulated content includes other resources being loaded (such as scripts, files, pictures, etc.), we inspect those as well and continue to do so recursively so that the pattern matching is accurate and effective.
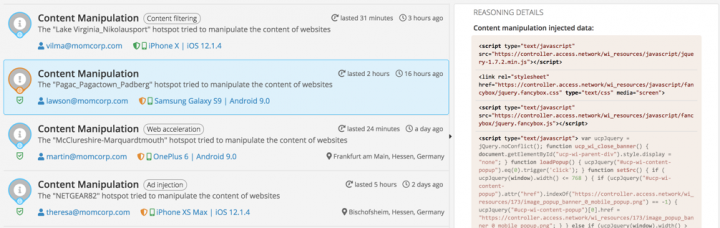
In addition to providing admins visibility over content manipulation incidents, SEP Mobile’s smart classification system is leveraged to indicate the specific type of content manipulation and its severity, allowing admins to go to the greatest risks first. Smart classification also enables optimal utilization of SEP Mobile’s automatic on-device protection actions, ensuring that organizations are always protected from these threats, whether severe or not.
Better Mobile Security Insights
As mentioned earlier, the amount of data and tools enterprise security professionals need to manage today is constantly growing, resulting in greater cyber security complexity. SEP Mobile’s smart content manipulation classification is a prime example of how we’re using innovative research, big data and proprietary technology to give security professionals threat accuracy and focus – so they can do their jobs easier and better. Such features help reduce the burden on overworked and understaffed security teams, while enabling more effective threat detection and response. In future articles, we’ll explore other incident classifications we’re developing to enable organizations to have a more precise picture of their threat landscape.









We encourage you to share your thoughts on your favorite social platform.