Symantec Mobile Threat Defense: A Snapshot of Mobile Security Incidents in Q3 2019
Risky apps used by millions of users and OS vulnerability exploits enabling hackers to compromise devices, were prominent among Q3’s mobile threats
Malware and exploitation of OS vulnerabilities seemed to be the name of the game for mobile hackers this past quarter. From malicious and vulnerable apps, with over a billion users, found in the Google Play Store, to a new iOS jailbreak affecting even recent iOS 12 versions, the mobile threat landscape in Q3 was a stark reminder of our favorite mantra: no endpoint is immune to security exploits.
As part of our quarterly threat recap series (see the previous quarter’s recap here), we take a look below at some of the major mobile threats that caught headlines this quarter.
Risky Apps
Attackers can manipulate WhatsApp and Telegram media files
WhatsApp and Telegram media files on Android devices could be exposed and manipulated by malicious actors according to new research released in July by Symantec. The security flaw, which we call "Media File Jacking", affects WhatsApp for Android by default, and Telegram for Android if certain features are enabled. It stems from the lapse in time between when media files received through the IM apps are written to the disk, and when they are loaded in the apps’ chat user interface (UI) for users to consume. This time lapse presents an opening for malicious actors to intervene and manipulate media files without victims knowing. A malicious attacker could manipulate sensitive information such as personal photos and videos, corporate documents, invoices, and voice memos. The threat is especially concerning due to the common perception that the new generation of IM apps is immune to content manipulation and privacy risks, thanks to the utilization of security mechanisms such as end-to-end encryption. However, this mechanism isn’t enough to ensure the integrity of communications when app-level vulnerabilities exist in the code.
Symantec's malware detection engines, which power Symantec Endpoint Protection Mobile (SEP Mobile) and Norton Mobile Security, detect apps that exploit the described vulnerability, across both managed and unmanaged mobile devices.
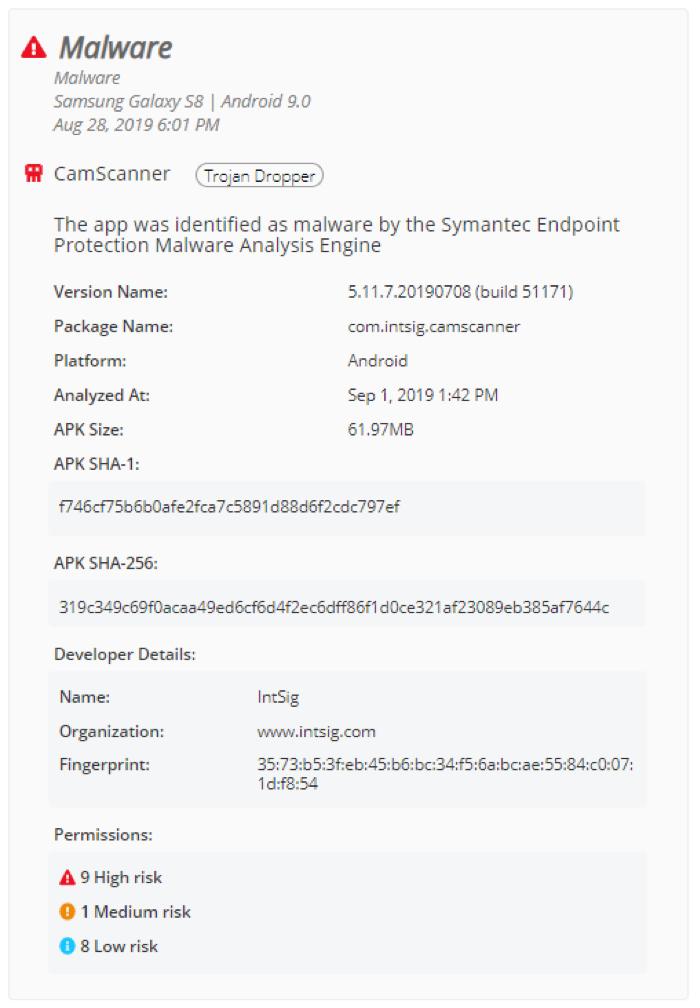
CamScanner app, with over 100 million downloads, found to contain malware
The free version of popular Android PDF creator app CamScanner, which has more than 100 million users, was removed from the Google Play Store after security researchers found a hidden dropper Trojan in it. Malicious actors can use the malware to show victims intrusive advertising or worse - remotely hijack devices and steal money from mobile accounts by charging paid subscriptions. Researchers said the malware was likely added to the app following the developers' partnership with a 3rd-party advertiser.
SEP Mobile protects both managed and unmanaged mobile devices from this malware. Our malware analysis engine detected the CamScanner app on several devices among our global user base.
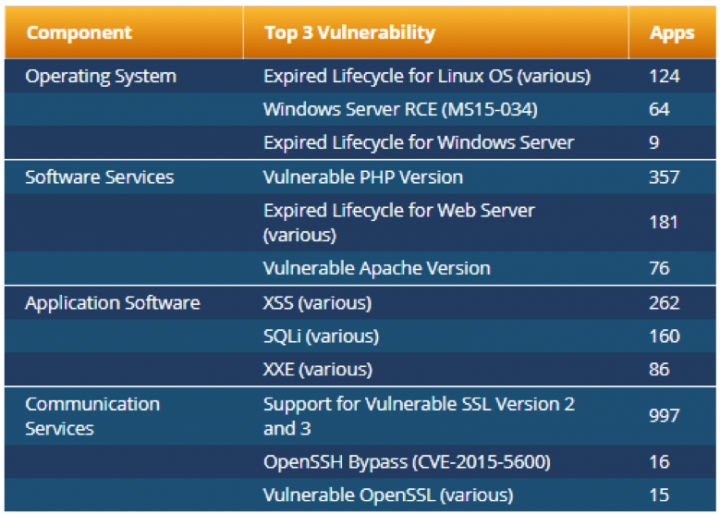
Hundreds of vulnerabilities affect Google Play apps, researchers find
App developers do not have a clear understanding of liabilities associated with mobile app backends that may leave data exposed, according to research that was presented at the USENIX Security Symposium in mid-August. Researchers analyzed 5000 free mobile apps in the Google Play store and found hundreds of vulnerabilities - affecting operating systems, databases, mail servers, DNS servers, and others - in thousands of apps.
The below data, from table 6 in the research paper, shows the top three vulnerabilities found per cloud layer along with the number of affected mobile apps.
* * *
Other notable app vulnerabilities we saw this quarter include: another privacy flaw in WhatsApp and Telegram involving the “Delete for Everyone” feature which doesn’t delete media files sent to iPhone users; and popular flashlight apps on the Google Play Store asking for between 50 and 77 permissions, most of which are unnecessary and can give developers access to personal data.
OS vulnerabilities
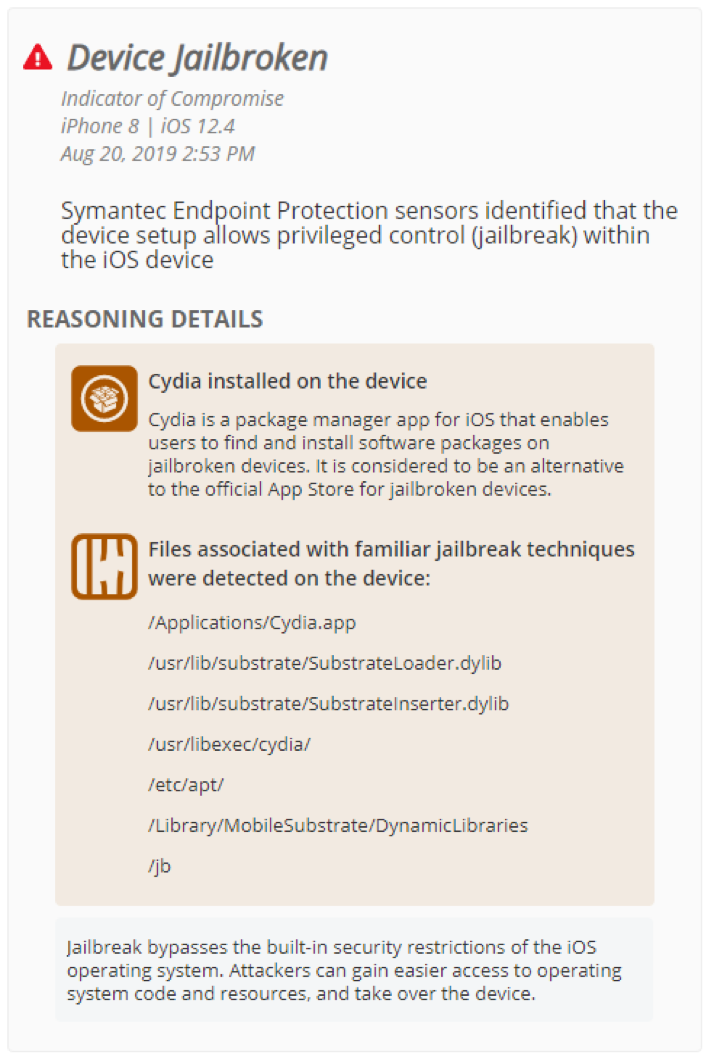
Hackers release jailbreak affecting even latest iPhone versions
In the leadup to the long-awaited release of iOS 13, hackers flexed their muscle to show just how much they were still in the game despite security improvements from Apple. After researchers discovered in August that Apple accidentally unpatched a bug it had previously fixed, hackers quickly released a jailbreak for iOS 12.4 released in June. This marked the first public jailbreak for a latest iPhone version to be released in years, making all devices of this version and below it jail-breakable. Essentially, malicious actors could exploit the bug to escape iOS sandboxing and steal sensitive user data from devices. After the issue was flagged by researchers, Apple re-patched the vulnerability in iOS 12.4.1.
SEP Mobile detected jailbreaking attempts on several devices running recent iOS versions in our install base (see example below). We ensured corporate data stayed safe using both on-device protection actions and enforcement capabilities, as well as by sharing telemetry with external sources, such as Enterprise Mobility Managers (EMMs).
Apple AWDL vulnerabilities allow hackers to track users, intercept files
The Apple Wireless Direct Link (AWDL) protocol, installed on over a billion Apple devices, was found by researchers to contain vulnerabilities that allow malicious actors to tamper with devices and steal data via man-in-the-middle (MiTM) attacks. AWDL is a key component of Apple services such as AirPlay and AirDrop, and it comes pre-installed on all Apple devices including iPhones, iPads, and Apple watches. In one of their findings, researchers discovered that a MiTM attack, which intercepts and modifies files sent through AirDrop, can effectively allow for the planting of malicious files. The fix for the AWDL bug (CVE-2019-8612) was rolled out in iOS 12.3.
Watering hole attacks allowed websites to hack iPhones for two years
In August, researchers at Google revealed a long-running iPhone hacking campaign that attempted to infect devices with malware using exploits delivered through compromised websites. The websites were well-known sites that had thousands of visits per week and were active since 2017. They used exploit chains that allowed hackers to break through iOS protections by abusing a range of security flaws impacting the iPhone web browser, sandboxing mechanism, and kernel. Nearly all versions of iOS 10 through 12 were at risk of exploitation. According to Wired, “The attack is notable not just for its breadth, but for the depth of information it could glean from a victim iPhone. Once installed, it could monitor live location data, or be used to grab photos, contacts, and even passwords and other sensitive information from the iOS Keychain.”
Vulnerability exploits leading to privacy and data breaches
This quarter also saw mobile threats involving unsanctioned surveillance activity on devices. According to reports, Pegasus spyware maker NSO group claimed that it has the ability to scrape data from the servers of Google, Amazon, Apple, and Facebook products. Moreover, in September, security researchers disclosed an SMS-based attack method that has been used by a surveillance vendor for at least two years to track and monitor smartphone users. The “Simjacker” attack abuses the S@T Browser, an application that resides on a device’s SIM card, to instruct a victim’s device to submit location data and IMEI codes to a third-party device.
* * *
Additional OS-based threats worth mentioning in Q3 include: the discovery of a lockscreen bypass on iOS 13 even before the OS version was widely released, allowing hackers to gain access to all contact information on an iPhone (Apple introduced a fix for this bug with the release of iOS 13.1 in late September); and a major flaw found in SQLite that can be used to run malicious code in the iOS Contacts app.
With a host of new iOS exploits emerging in recent months, it may come as no surprise that these exploits aren’t as valuable as they used to be. Zerodium, a large exploit acquisition platform, has assigned a higher cash value to Android zero-day exploits – at $2.5 million, surpassing iOS exploits at $2 million. This marks the first time an Android zero-day has been valued at more than its iOS equivalent.
* * *
The release of Android 10 and iOS 13 this quarter brought with it new features and security enhancements for devices running these OSs, but mobile users should not be mistaken: new versions do not mean non-exploitable versions. The threats highlighted above and their growing complexity require enterprises to be vigilant about their mobile threat landscape and take security measures to mitigate the risk of privacy and data breaches.
SEP Mobile customers can stay on top of the latest mobile threats through the Mobile Security Headlines tab in their environments. We’ll return with a highlight of next quarter’s top threats at the end of Q4.

Symantec Mobile Threat Defense: A Snapshot of Mobile Security Incidents in Q2 2019
Threats associated with risky apps, iOS-device hacking and mobile phishing were among the major incidents









We encourage you to share your thoughts on your favorite social platform.