ASUS Software Updates Used for Supply Chain Attacks
ASUS update system hijacked to send out malicious updates to as many as half a million computers.
What has happened?
News has emerged that tech company ASUS has been delivering malware through its automated software update system. Based on our analysis, this supply chain attack started in June 2018 and continued through to at least late October. It may have affected up to half a million systems.
The Trojanized updates contained a form of backdoor program which attempted to connect to an attacker-controlled domain. The updates were signed with legitimate ASUS digital certificates.
Am I protected?
Symantec detects the Trojanized updates as Trojan.Susafone, Trojan.Susafone!gen1, Trojan.Susafone!gen2, and Trojan.Susafone!gen3.
What happens when the Trojanized updates are installed?
The Trojanized updates search for specific machines based on their unique MAC addresses. If specific MAC addresses are found, the installed updates attempt to connect to asushotfix[.]com. This domain is currently offline.
How many victims are there?
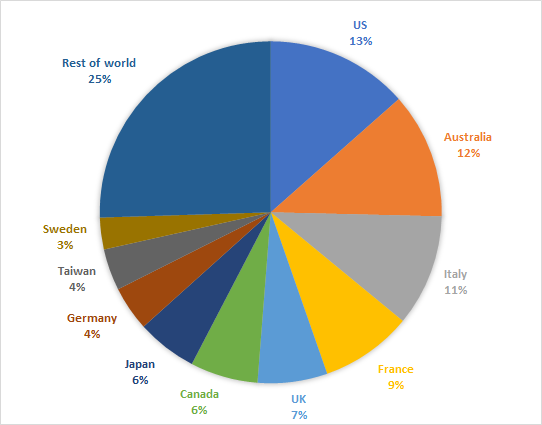
Symantec telemetry shows that at least 13,000 computers received the Trojanized updates. 80 percent of victims were consumers and 20 percent were from organizations. Our telemetry shows an even spread of victims across the globe.
What is the motivation behind the attack?
The attacker motivation is unclear at this time.
Who are the attackers behind this attack?
This is unknown at this time.
What is a supply chain attack?
Supply chain attacks attempt to exploit third-party services and software to compromise a final target. Hijacked software updates are one of the most common forms of supply chain attack. Similar campaigns in the past include the CCleaner attacks and the Petya campaign.
Symantec noted in its latest ISTR report how supply chain attacks increased by 78 percent in 2018.
Thanks to Kaspersky for sharing details related to these attacks.







We encourage you to share your thoughts on your favorite social platform.