Over 150 Fake Jio Android Apps Offer Free Data but Deliver Only Ads
Apps aggressively display advertisements and are designed to trick Jio users with offers of free data allowance boosts.
Symantec has uncovered 152 malicious Android apps being circulated online that claim to provide free data boosts for Jio customers. The apps masquerade as apps from Reliance Jio Infocomm Limited. Reliance Jio Infocomm Limited, also known as Jio, is the largest 4G network in India, with more than 300 million subscribers.
These 152 APKs were developed under 21 different package names, all of which claim to offer a free daily data allowance of 25 GB or 125 GB for a period of time ranging from just one day to one year. However, users who download these malicious apps will not receive any free data boosts; instead, their devices will be used to generate advertising revenue for the developers of the apps.
Jio customers with JioSecurity installed on their devices are protected from these malicious apps. JioSecurity, which is powered by Norton Mobile Security, is available to Jio customers for free from the MyJio app.
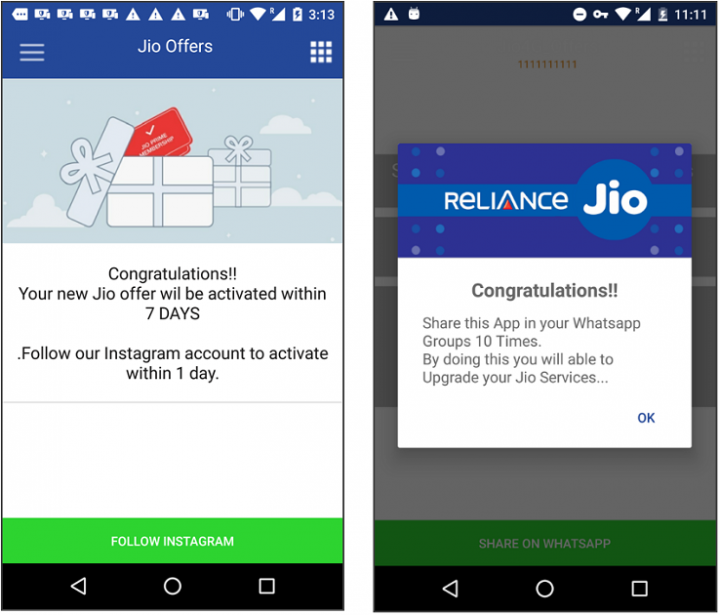
While the fake offers promised in these apps vary, the tricks they use to deceive users are quite similar.
Trick 1: The art of imitation
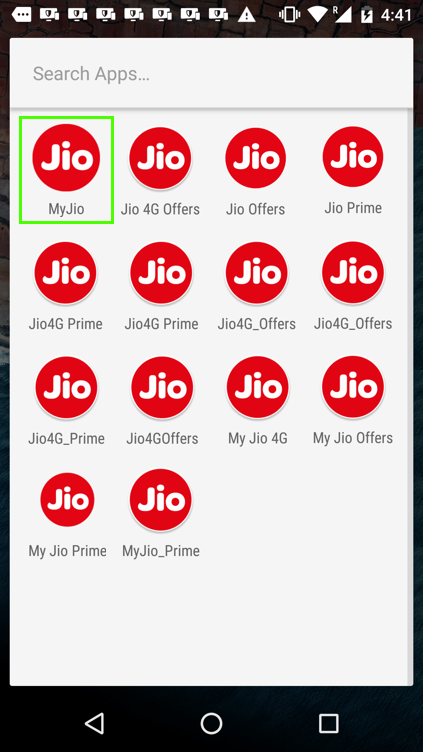
The icons used by the malicious apps are identical to that of the legitimate MyJio app (see Figure 1) and the names used are all variations of the legitimate app name (MyJio). These imitation tactics alone may be enough to fool many users into installing one of the fake apps. Coupled with the offer of a free data boost and it's easy to see how these fake apps could be tempting for users.
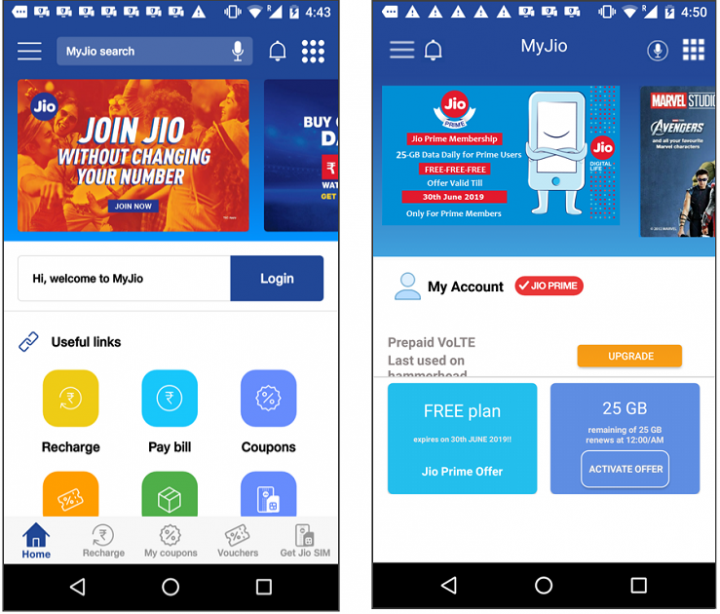
Upon launching the malware, victims are greeted with a splash screen that also resembles the original app. The user is eventually shown the malware's main screen which shares the same user interface (UI) design and structure of its legitimate counterpart (Figure 2).
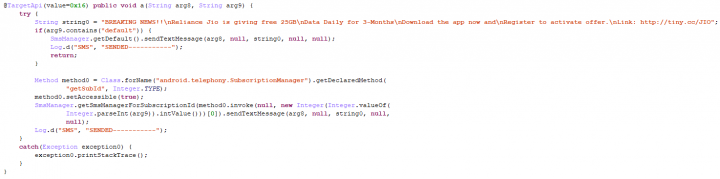
Trick 2: False impression of progress
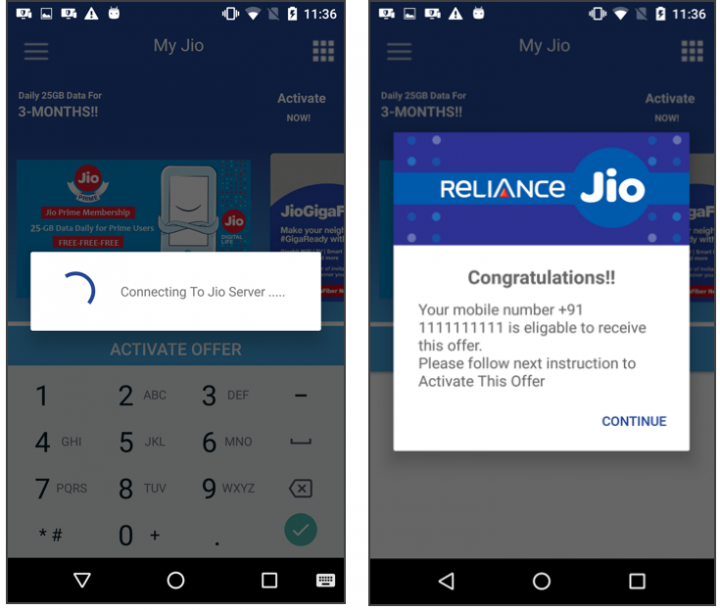
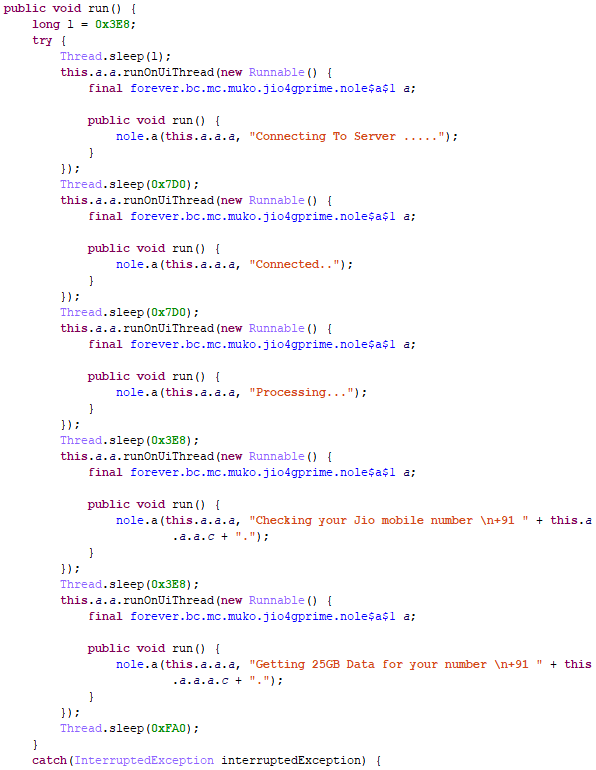
On the fake app's main screen, the user is shown a dialog box or a text field, requesting the victim's cellphone number in order to activate the free data boost offer. After entering a 10-digit cell number—regardless of the validity of the entered number—a dummy loading spinner is shown, giving the victim the impression that a request is being made to a server to check their eligibility. In fact, the malicious app's source code shows that no real connections or processing is taking place while the spinner is displayed, and a sleep timer has been added to extend the time the spinner stays onscreen (Figure 4). After some time, the user is congratulated and informed that their number is eligible to receive the offer, after they follow some more instructions to activate it.
This ploy was used consistently by the malicious apps, always making victims think they are just one step away from getting that elusive offer.
Trick 3: Spread the word
Next, victims are asked to share the app with 10 contacts via WhatsApp in order to activate the offer. Other variants of the malware ask victims to follow the developer's Instagram account or a Telegram group (which are listed in the app). There are also some versions that ask victims to share the app via SMS. Worse still, some of the apps don't even bother to ask the victim and just go ahead and send the SMS messages without the user's knowledge (Figure 6). The messages contain a link to download the malicious app and are sent to numbers in the victim's contact list.
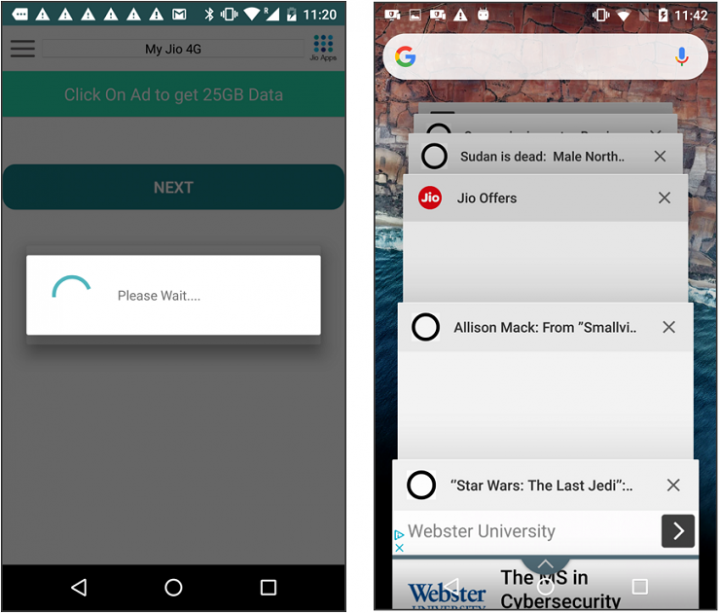
Trick 4: Aggressive advertisements
The malicious apps' final trick is displaying advertisements. Some variants attempt to trick the user into clicking on an advertisement in order to get the offer. Other versions spawn as many as 16 processes automatically to show different web pages to the victim. A more aggressive move still involves advertisements being spawned non-stop by some versions of the apps, which effectively results in an infinite loop of web pages popping up on the device.
From January through June 2019, our telemetry shows that these fake apps were installed on more than 39,000 mobile devices, with the majority of them located in India. The total installation count of these apps, however, is likely to be much higher than 39,000 since victims are requested to share the apps with their friends and families.
Protection
Symantec and Norton products detect these apps as the following:
Mitigation
While the lure of free data boosts can be tempting, we advise users to always validate with the official parties through proper channels.
Stay protected from mobile risks and malware by taking these precautions:
- Keep your software up to date.
- Do not download apps from unfamiliar sites.
- Only install apps from trusted sources.
- Pay close attention to the permissions requested by apps.
- Install the JioSecurity app to protect your device and data. JioSecurity is an advanced mobile security app powered by Norton Mobile Security. JioSecurity is available to Jio customers free of charge from the MyJio app or Jio.com.
- Make frequent backups of important data.
Special thanks to John Hou and Liu Zhe for their help with this research.
Indicators of Compromise
| APK SHA2 hash | Package name |
|---|---|
| a4g.muko.bhadvo.jioprime_4g | 250af63da1463ff5483cf1f97acc4f6c7384f7e228ae6e82751cb79c8cf0e28f |
| a4g.muko.bhadvo.jioprime_4g | 2fb9da99afd0736567ca900e1aaf19fafdca1a9e0eec2b8c69f7fcc799baebcb |
| a4g.muko.bhadvo.jioprime_4g | 9dfcfb6fed8b1f9136a841b4fe535dfb1c8de54622ba683b5e6ecf8ec992426c |
| a4g.muko.bhadvo.jioprime_4g | ddf726bd6369c422e0ca3f8d9d10ff316674f8490b3a1e648c41281ad93167c3 |
| a4g.my.afor.offer.myjiooffers | 077cda0052f1baafc6431c1791b03d6e51b989a9e6b9e9e72cc28b885f03913c |
| a4g.my.afor.offer.myjiooffers | 07f19961b59a93b4286e9a5be2b6803490b1819ceb710de4959d6a5ee401cd9a |
| a4g.my.afor.offer.myjiooffers | 0b79591d394d2a1e6507aae55320f5a10635c54620df769b118d5e01d3df4dba |
| a4g.my.afor.offer.myjiooffers | 0cfe274a55b84d184f7c5504893e457df678a47e2361c65930de971056277c2f |
| a4g.my.afor.offer.myjiooffers | 611ec47394fdc7efa85ba1c33abc6e63bd3805cf0b0484afcce9b8171409c067 |
| a4g.my.afor.offer.myjiooffers | 68995253f1d6424297050c65d12f3ec79b8efbfd0f91568eb142f2e77bb75e2d |
| a4g.my.afor.offer.myjiooffers | 7a9ff29eb64e27a37923f3cf4efd89c4e29a179dd7690536b1f5a8ada2e6e5c6 |
| a4g.my.afor.offer.myjiooffers | 928bcc3b54d7974ce7d9eb24d98d5d8167b6502cfcbd258647a2fb3f16e76db5 |
| a4g.my.afor.offer.myjiooffers | 9f432f4ff22729021099580b3bc75bdc3bf32cc0cc5e90df9f5c711f8147541f |
| a4g.my.afor.offer.myjiooffers | a48fcd9c574b674ebf9677206676ebe081dfb21a91d25c7f55c4c197b0d31a85 |
| a4g.my.afor.offer.myjiooffers | c57d16adec9c4258462ee73b6621ea57bf7b033a77d483c9b8caa6bbcce29353 |
| a4g.my.afor.offer.myjiooffers | cc79865b42073c0ac5087c570b4dc3ab657e4bfd6bf483f64131e47620e322c8 |
| a4g.my.afor.offer.myjiooffers | e1b5dd5b21c93b0d0b1008cd8bfa801a1090236611a61775775bce03a10787b0 |
| a4g.my.afor.offer.myjiooffers | e1ccc7a8ade818b6bb74a135a8b70ea139ce2ca475c62fb9ceb7db2f07c81670 |
| a4g.my.afor.offer.myjiooffers | e7ae8d3660fa361838ead5c2f7b1dea989b4e7a41c3d239643d0f8ca661fd2ef |
| a4g.my.afor.offer.myjiooffers | e7aef086f7438f0fe04d04e0e6a000ab1c3ebe9466a74765a8c1f68a0b5736ec |
| a4g.my.afor.offer.myjiooffers | ffd1969b43619d63e0416aaec9c6c552be3fde41423dfd849bdc5c65399a5034 |
| ambani.muki.joi.jioupdate | 077d809fad0416d9522a7639bdb310f80da09a3377b38a408ccbb3fd9ccd2498 |
| ambani.muki.joi.jioupdate | 1c4f1e26e49f0782ec1a170e2a87f0b9ab0a7e5024691fc84b64be4582d6d68e |
| ambani.muki.joi.jioupdate | 57bbe5b12d222c61aed67ef7b104e422173727af46ff59d04ca18bf23d733391 |
| ambani.muki.joi.jioupdate | a86e482012593d5bbc2277ffdf2e5d43650a0a57ce201bcb2db3b701b2155f7f |
| ambani.muki.joi.jioupdate | ff1a4f1342c24fa1d44e88ff6e0e9b6cac59472335594bc29a3b65f3da9920e2 |
| ambo.muko.chutyo.jio4g_prime | 2385cc94c8161211b7b179e3bb9a8aaa5b67d6edbfdf23a1f8f091c59bcd09f5 |
| ambo.muko.chutyo.jio4g_prime | 3e4c1653cee9522c21f77a7bd4d1222a3b8d86c231165eba83a664a888a203ee |
| ambo.muko.chutyo.jio4g_prime | 96e8a8dbd4d9e4104031b689cfef067e908f1dc6f727bb21f952e313a8b35976 |
| ambo.muko.chutyo.jio4g_prime | 98a67bb7d8765187bfa615fe8b33f8fa94bcb4c0460e652be4051ea5324c9b91 |
| ambo.muko.chutyo.jio4g_prime | dba05e99c9850767d4d5d3596f3bad6084568639556f1838c1dae1de3fb42fea |
| ambo.muko.chutyo.jio4g_prime | e0e239f7d0d5e331fddbd87c666461481471bbb5224e59fd6333a8a193aa95b8 |
| apnafds.time.aaya.myapplication | a28ef69a4d1bacbfa41ce572322602e40be5800f95f483a39c23ba52e25e752a |
| apnafds.time.aaya.myapplication | a8a142a4651606aaba151f72f1fe3fad5a0b4f2f7b7888413dc4df112ce3c90b |
| apnafds.time.aaya.myapplication | aca859dcd527d74ced7a466caa134426bc0665451836f7da9cc2d8ac69718532 |
| apnafds.time.aaya.myapplication | b2a534fa5456d27b56e4968431a39ae6c3e864dc47d6710201827d004c1aefcc |
| apnafds.time.aaya.myapplication | bdf9a9e962107987176a18596494ea7b50a6f2338c4516f910d3313a0acdcfc9 |
| apnafds.time.aaya.myapplication | d0459088eac5561759d5293887d915fab9fadbec952a6858c9e2865771b503f2 |
| apnafds.time.aaya.myapplication | fe1cbf6ee86e2c374f7bc6a13cf6232def06c76d6bc8c654b3d9173e5db08b72 |
| bhadva.chromva.jio4goffers | 1178a46fc847dd4dee30cc8d648bb1848fd69be23b2c52adb2586ce8c31acdfe |
| bhadva.chromva.jio4goffers | 482561822f21b807cfc2809d5125ccc22d5fe49c59b0d26395572a36985bd4d7 |
| bhadva.chromva.jio4goffers | 7fb502ce2f6c8edcd4a801eeee4393c2b27d4988a7e1261df98facc7c72868ed |
| bhadva.chromva.jio4goffers | 991b4ded04820306eb59e3086c967e7473b5f547b0a0c1003ca3347a84b4bef6 |
| bhadva.chromva.jio4goffers | ba0a5b1fa3460fb4b4a4cb6907f6f384acb312009df66eae94942e2a999400e1 |
| bhadva.chromva.jio4goffers | d3d8a1505549d876dbf95df8b00f623cd3074873231b3374a7dd7812de8ecc06 |
| bhadva.chromva.jio4goffers | ed1c02b3b39e5af561470a0f4e7fab227f6d7b826cbc46c1273bf1469ce6fb5c |
| choice.my.offer.myjiooffer | d83755082ad0a421723299dce53516004d16709ba37b5d6ad1315f8fe426462d |
| er.upgrad.jio.jioupgrad | 97137e7e9cd67c6032713d73724d6bc48cc047ab0fe80a718667333074df6e88 |
| er.upgrad.jio.jioupgrader | 039f1fe4b0bf032964d48ace4f3d71f1dce011fafc24ac9b39be59095be8c82c |
| er.upgrad.jio.jioupgrader | 06f878193b2a69c44cdbbd11f3de1ed8ea0ab40213b620f1a1c4821ce78a5661 |
| er.upgrad.jio.jioupgrader | 0beef24cd6efaeeb2d4e637fb4996cad24cf53f234753f83a2faea5034d653bd |
| er.upgrad.jio.jioupgrader | 0c6b20e0327b1c165e9476d67de719114c770158b62ac64964f2b085b71c22f9 |
| er.upgrad.jio.jioupgrader | 108e4a0f7d5b1d3c0f4b80a3e8c9791070d2acd5a58c453e9ca47901754f39d5 |
| er.upgrad.jio.jioupgrader | 1943021a150f3e5687db9170d09066c3bb14fe384087bb89c85d5ae137870392 |
| er.upgrad.jio.jioupgrader | 1d27dd99a3a686d0e2928e5d36fc4d9669f34ee919f8d3465cb08d44df9501ad |
| er.upgrad.jio.jioupgrader | 36cce1830c9541a8faa46c0916f6a40ef047df1ef7174bb47cdd4158781d4dac |
| er.upgrad.jio.jioupgrader | 3d687e4728e6dbe42ee3c26a7307e7c554dfe900d61571a9b93fa53f0aa1bf22 |
| er.upgrad.jio.jioupgrader | 4219847b3b7c6dff0c4aed6350e727f938d513c7d1fa7b77a5cceeebc182d108 |
| er.upgrad.jio.jioupgrader | 45d05e67df7fa53cb511fbd406ee96eeb6bd0423c6f87b160b559cb34baba42d |
| er.upgrad.jio.jioupgrader | 4e1d010aa0a51442f40f0277b107e3cb6eaccf26d8d57c604c799928a77583c8 |
| er.upgrad.jio.jioupgrader | 5218c91252beafdadad70d25454a34164aaaf4fa172547788f8c6b538303674f |
| er.upgrad.jio.jioupgrader | 5267d5192cc13f9a15c6dae3774cc46f73f4c94c1e6d7cf536d174f4bedb553d |
| er.upgrad.jio.jioupgrader | 54216dbf24dad5d651d8d0fb509eaef97a97ed008ee8f7af3961a948ae4cd9e2 |
| er.upgrad.jio.jioupgrader | 5440ceb8584f0b435ff88b56e352a3ac27684e970a3d990c3d753d03798282cd |
| er.upgrad.jio.jioupgrader | 54b7e242b408ed91d746a05cddfb53cab80fa8332d50c1f96333cf068bca4628 |
| er.upgrad.jio.jioupgrader | 56292a49c2a799aacf7a301baea269c083a4cbf2856b8971c1df5e056390dd64 |
| er.upgrad.jio.jioupgrader | 5eda69239ab50bcaca6e70901f5c3896868bd278ab8fc84574d598f040bd71fd |
| er.upgrad.jio.jioupgrader | 5f2929454f95342626b4884fb454f56f5147d6013b8e236b8185d99d6ac67d4a |
| er.upgrad.jio.jioupgrader | 610c3d8a03a4418aebd89885b3a959f9b2c9908f54f8657e1842f7ffbbb0a103 |
| er.upgrad.jio.jioupgrader | 698ea0be9be32997dceede6044cb7d3415366850b0371f88ce02db0034ec6d2a |
| er.upgrad.jio.jioupgrader | 74ee1deb6c95ac735db76ed444614580e4839be03f3628e321f58fff620b1bda |
| er.upgrad.jio.jioupgrader | 7f4cea3b6bceb4aebb45a8f1c6e528f90eec1a87009f18d93de51b32fc85034c |
| er.upgrad.jio.jioupgrader | 8079126d6078386f0d592a3ea361a2639019ad0089a3a833a6f749da61126f56 |
| er.upgrad.jio.jioupgrader | 815c4043df04a57bd25da3a3a3db50899bed663f05eba18e329562d7948f9bcb |
| er.upgrad.jio.jioupgrader | 82a98329fd539c8b54bf688e2aae3743b262cc6a5fc08b8e4122496d0112e777 |
| er.upgrad.jio.jioupgrader | 8dca06dfeaa22b01a493a3ea4590ccee6266bd0afa5cc234f7b978f72be5bae5 |
| er.upgrad.jio.jioupgrader | 8f8e4699e25c11027c1388d4e0fec8d79d06e4e4fe8bffd7eb93f9d4b76e2c97 |
| er.upgrad.jio.jioupgrader | a471f0134cefd3b41c307203f35ce286099dfc96b2f38fe89b003e2af282aeb6 |
| er.upgrad.jio.jioupgrader | b0398497a3cc0aabe808a1d051e9fd0b3bd2629b63237522ec5182e35e199534 |
| er.upgrad.jio.jioupgrader | bb9fa282ba2227907d89d055aa74ad608c6b1d81bfd3057b8c5f57b5e0e9d0c2 |
| er.upgrad.jio.jioupgrader | c0ecf7da3fec446efbd856a3db6665b7f31017b8173f512fd655ce61703fab51 |
| er.upgrad.jio.jioupgrader | d4603a231e882afb62feb82ff8a3f9bd4633c8dd06c7cc0e48dfc6cd600b7080 |
| er.upgrad.jio.jioupgrader | d51dea6bf3b5ff76fc54ab4b989647fbed0d6592684bb88e0f03951c598454e2 |
| er.upgrad.jio.jioupgrader | f032d0cdf938c2b9a35a1042282531af3ad5f071c4c4fa58afe6eddf7febe399 |
| er.upgrad.jio.jioupgrader | f8df5d3851588d43c157a347c47a0fd234c49c45b6e9741b45c19bd7b46f1a7c |
| er.upgrad.jio.jioupgrader | fbe4a61a104025101e92a6a38ed6583e63145fffffeca935b6098228c10f520d |
| er.upgrad.jio.jioupgrades | 99a76219ef86a6c78d651b71c31f8e868e0d8f62728f47249c84c95b66a06866 |
| forever.bc.mc.muko.jio4gprime | 0d2aa38c801d8eb86d5aff054d462805548480f12dd6ca3ae8fd4816441996fc |
| forever.bc.mc.muko.jio4gprime | 9b0f6dd2e9c33bb926bf887bb5e0393215061eb8bfd1cbe9c14a32564f9dae09 |
| india.jiooffers | 34622994dd927edcb67f8ead44e548fc66964d144df5dbc930f12a6da9984c00 |
| india.jiooffers | 47f8d512c17627625806a30929462ffa731ebbef96f8f8554d6cf56f5d7c3bbd |
| india.jiooffers | 4be2b3dcfbdef944fcb82bec8ebec45709efb907066d1b3bd3797d5f098b1c39 |
| india.jiooffers | 7b5346196e0dc9b2965e994c82cf8d2fec47a7ca96abdba8bad6c644298d52de |
| india.jiooffers | a25e806b7e9c84e29afbdca92d037a8619137db9320d465c7558afde5d7357d1 |
| india.jiooffers | b894574fc6df3b5007587123c9ba098d1be82bd6f9942170995fb518f1f8854d |
| india.jiooffers | c38ea8d6dd56b4d4e304a0c230d6982e41464bc4288b03e5bf4e80cd326b6d8a |
| jiio.offerva.com.myjiooffers | 0fcb05c78d7d72f9f256433457db3cb42b3982dda2779c4307e322c8eafa528c |
| jiio.offerva.com.myjiooffers | d98b7ba399ae17165af79d0267062c2c58cd7e48c7ce8dd3e97d07c030d58349 |
| kiol.offerva.my.jio4goffers | 4ef2fe3774c7e85f31d56e1678f761c42dcbcddc3fe5a86d0bf8d229558316a8 |
| kiol.offerva.my.jio4goffers | 6c04f725db620a1a89b54befe156c0090bcedb39b1d13d6010b760c19c6953af |
| muklo.chutyo.hato | 0e6288743395199325c7fb4aff7c2215d1efed7d929354ae5bd102dc9efc7623 |
| muklo.chutyo.hato | 8295e3b045eac221d2db957928c6dc6dede5893d87556785850cfe3979073735 |
| muklo.chutyo.hato | d609e5374609240bd8d77fbf3a08df32914686628aed51ba414d220445a8fbe4 |
| muklo.chutyo.hato | da39063b1ab60f4a894e7450723ee6c33a77ed7120604fa84411ac47657a8d70 |
| muko.bhadvo.che | 886209c31ffd393d15b4603dad57433329cf60ef064019013e54fd49b2fee8cc |
| muko.bhadvo.che | e0ceeb16e18bdf6284d7e46a1df105bc4dfe7530d20e2cc107441b16c9333c58 |
| mukodi.updli.upgradingjio | 20f0de4cfec7fce552b02926c33d7a3690bb0dda0b0f0a8405703c1f711e3614 |
| mukodi.updli.upgradingjio | 4e9be9727ecfc4c93588563ed69397b3e292bf8f3bcae02f649bf9de5a6dac35 |
| mukodi.updli.upgradingjio | 7a35a3cec5279fb6ede4f3b1708b3c9128ab284a298868375552e35e4de14ca3 |
| mukodi.updli.upgradingjio | e33452e42e4982dfc609a5ed63ba4853c6476472c4d01032abfa92a9c310c8e4 |
| offersss.prime.my.jio4g_prime | 3928ab806f4854987d0b50d17f1cef6a36ba5668e56ff61114697756ca043884 |
| offersss.prime.my.jio4g_prime | 3cb4c3fb4dd043a0f33148051000192a6b84df06350ea15ddc9f69e2077b8754 |
| offersss.prime.my.jio4g_prime | 599e482ef5208f53a5b2da7e1da4bf98123ebaf5f77f5fc0d413cdf4f56d77e1 |
| offersss.prime.my.jio4g_prime | 5c68f00ba107db8cffda99dc13e772f609d4e09a2b46c8220936bdf21c998805 |
| offersss.prime.my.jio4g_prime | 896baaa16c2c41584266f6cbbf0d6f70bc0cc4874691294110a5702370e1966b |
| offersss.prime.my.jio4g_prime | 9cf52fbe6380d925ba84078ad39a3e88cb1bef3bcde98d329c8400b78376d7b0 |
| offersss.prime.my.jio4g_prime | bc1d4d48c048f0d65d0b18cbee473fe1cd110e18b303edca69cf0ff76c435b9d |
| offersss.prime.my.jio4g_prime | c5e1dcaa2759082b48434091185d8aca0951b5e350a4a12566854e497d72c232 |
| offersss.prime.my.jio4g_prime | e1dddaa9afca116ad8e69e22e4cc4bcccc339dfe44a571073c29a7b4f8ff89dd |
| op.voiice.a4g.anew.new4gvoicev | 41a0440c8a5c7ebf223d648deace4b43a00fe2a1540dc86df456b3b823e9dec1 |
| op.voiice.a4g.anew.new4gvoicev | 7091d3b58d9680ab257ba328048d1e4142bbbade4e424062a1ed6af26b92005b |
| op.voiice.a4g.anew.new4gvoicev | 8c393609732d6f8cf2e10a75aebed11f3a869791461469a9a9927f8a77be94ed |
| op.voiice.a4g.anew.new4gvoicev | 8d792f1fd5e89e345b988dd7c1166a3148af0135912771f6394fecaa8f8656c9 |
| sdffn.bobl.offerva.myjio_offers | 15fe57d22eaff1f3a10ff2020fa5a1c639a3665b22984e1cb2bd76a2855facf7 |
| sdffn.bobl.offerva.myjio_offers | 3640f0c14535157938c78571fac47e700d3cfec1d56ec399a90eeb83a35461f8 |
| sdffn.bobl.offerva.myjio_offers | 531074d578e0cd9e6cad0cb8216dad0972bce20a56f531d26ea2a7a1ed9e35b6 |
| sdffn.bobl.offerva.myjio_offers | 5caff86bea2a6a3aceeba21e785bc4b3c9fd68a18a9ea90d4b641801678222f2 |
| sdffn.bobl.offerva.myjio_offers | 5e391b2329e8f9d8d55a8c7e2a78b6793cb9526190a7398b164cdaf78ed45ecb |
| sdffn.bobl.offerva.myjio_offers | 618ae51758556ea2eeb4269e834b6d16cbac0ea91d9ef8e4ad82a2dd7630c938 |
| sdffn.bobl.offerva.myjio_offers | 621f18abad4e83417111b0506fd8380427832595aaee7d85ab6de54335a9814d |
| sdffn.bobl.offerva.myjio_offers | 73ac13d43ad25d3bf3f2034b9e29bf20bd448f4a5e1808f985cdca56aff041d5 |
| sdffn.bobl.offerva.myjio_offers | 741ca21e33b458bf7f3f6c58d3d4bbd05700ab5766172670531a5524b270546b |
| sdffn.bobl.offerva.myjio_offers | 81e8e9719e9c0d67741a963c5d787f1fb6afc091da8cd16338d5eb118bb09f4d |
| sdffn.bobl.offerva.myjio_offers | 82330c589f942eca824ea3fb7795f7fdd928cde39e13acdde6cd884d5df01ba4 |
| sdffn.bobl.offerva.myjio_offers | 86297dda9c090b2a8f326039636a5eae79f61136c49a859653a39c27cc778656 |
| sdffn.bobl.offerva.myjio_offers | 93deae413965e8b7a667232290a33fd80223d4d132be92ed44329a8c71c36632 |
| sdffn.bobl.offerva.myjio_offers | 9d680dacba03d7a71d18c35bf05b63cdba3813f500aec45f70ead2472a830768 |
| sdffn.bobl.offerva.myjio_offers | a379488355949d412158405d3e1074959c96050eb4812b171f520d0046283ca2 |
| sdffn.bobl.offerva.myjio_offers | a7aec25fa48f10fe89e1fb167a9642f871e588e0ada6a54ad2fc370f690144ee |
| sdffn.bobl.offerva.myjio_offers | d3376fe88e73e649ef4d7040c0990b25119cdb98ffda34ef81ffd4c0519b382c |
| sdffn.bobl.offerva.myjio_offers | daa7b780e7a2be97378f16376e89e9adc34e7cebb3a1d1e95f82e654a88bd83a |
| sdffn.bobl.offerva.myjio_offers | f04defc5ea54d60699e7a2190d8e6724a4b9a672cdf60a5052061b5a6dcd7bf7 |
| yours.offety.primu.myjio_prime | 1d171622cc4b125f4d090818b8a48fafa2cdeadc542d2188435b70d08d7aad6b |
| yours.offety.primu.myjio_prime | 697d7ab6af5da20c95988ca1e0a4da62c8710584091ec4d242e9152279692122 |
| yours.offety.primu.myjio_prime | 76ec425e4fd181e44b41c80b835ee820814390d8398d0f9ea130d317efc252a6 |
| yours.offety.primu.myjio_prime | 80103be961543b0161d9ad7f673616a6549a82f58be3b54d019c14bf7f99452e |
| yours.offety.primu.myjio_prime | 85d596ea625adc3240036a4178e6f32bc1b77b7daa5a085eb4d9b85c0f24d972 |
| yours.offety.primu.myjio_prime | 9b577362b4dbccd954c60f3af5a0e585f2034f2e59921f6870ec6f1da47aa6f0 |
| yours.offety.primu.myjio_prime | afe5f021d088426e7ccecfaff4561644dc05a673ae25e18df8e7acf60244ccf2 |
| yours.offety.primu.myjio_prime | b064fa7369ab9c229bbe8b8c0cba7bc9a8737783de7b3186122e1b6f798292f2 |
| yours.offety.primu.myjio_prime | d4e767ac41bd85f5aeb6bb7d2c57e6102560471daf235acb0bdb9f0993ee5efa |
| yours.offety.primu.myjio_prime | ded4473d66c5b3f6be482d34cd8d555cc7906f7362cad926c8bdd4778dd49e46 |
| URL | |
|---|---|
| http://instagram.com/_u/india.tech.news | |
| http://instagram.com/_u/myindianews |
| URL | |
|---|---|
| http://telegram.me/UnEthicalHacker |









We encourage you to share your thoughts on your favorite social platform.